The Underestimated Importance of Computer Device Lifecycle Management in the Workplace
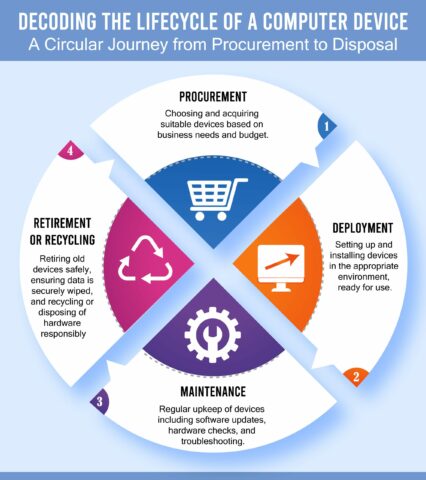
In today’s digital age, the lifeblood of any business, regardless of its size or industry, is its collection of computer devices. From desktop computers to laptops, servers to tablets, these pieces of equipment form the foundation upon which modern organizations function, enabling them to maintain their operations, execute critical tasks, and deliver products or services to their clients. However, managing the lifecycle of these computer devices, especially for businesses with an extensive collection of IT assets, can be a Herculean task, presenting a unique set of challenges that require a focused and strategic approach. This is where computer device lifecycle management (DLM) comes into play, offering an effective strategy for dealing with these challenges.
DLM can be regarded as the unsung hero in the IT realm. Its importance is often underestimated, but it is critical to the effective functioning of businesses in the contemporary world. In this in-depth exploration, we will shed light on the importance of computer device lifecycle management in the workplace, delve into the different aspects of DLM, including onsite warranty options by the manufacturer or third parties, considerations for deciding when to replace or repair a computer, and guidance on the ideal duration computers should be used in the workplace before being rotated out for new equipment. We will also examine the concept of product end-of-life (EOL) and its significance in the lifecycle management process.
Onsite Warranty Options: A Shield Against Unforeseen Problems or an Unnecessary Expense?
The first pivotal aspect of device lifecycle management to consider is warranty support. Onsite warranty options, offered either by the original equipment manufacturer or third-party service providers, can serve as a safety net for businesses, providing an extra layer of protection against unexpected device failures. But, like any other service, they come at an additional cost.
Businesses must carefully weigh the benefits and drawbacks of these warranty options. Is the extra cost of the warranty justified by the value it brings, or is it an unnecessary expense that can be eliminated? The answer lies in an objective evaluation of the potential cost of repairs and downtime caused by device failures, in relation to the cost of the warranty. For businesses heavily dependent on mission-critical devices, any downtime can lead to substantial revenue loss and affect their credibility. In such scenarios, investing in onsite warranty options can be a wise decision. However, for those businesses where devices can be easily replaced, and a robust backup system is already in place, onsite warranties may be an extravagance that can be avoided.
To Replace or Repair: A Balancing Act of Cost, Age, and Business Impact
Another critical facet of device lifecycle management is deciding whether to replace or repair malfunctioning devices. This decision can often be a tightrope walk, as it needs to balance the age and specifications of the device, the comparative cost of repair vs. replacement, and the overall impact the device has on business operations.
If a device is outdated and nearing its end-of-life, pouring money into repairs might only offer a temporary fix and still leave the business at the mercy of inevitable future failures. In this case, replacing the device could be a more economical and efficient choice. On the other hand, if the device is relatively new, with high-end specifications and a major role in business operations, investing in repairs could be a viable and cost-effective solution.
The Ideal Duration for Device Rotation: Striking the Right Balance Between Usage and Technology Advancements
One of the most frequently asked questions regarding device lifecycle management is about the ideal lifespan of a computer device in the workplace. While there’s no one-size-fits-all answer to this, due to variables such as usage, maintenance, and upgrades, a general recommendation is to rotate out devices every three to five years.
Following this guideline helps ensure that the devices used by a business are in tune with the latest technology, reducing the risk of relying on outdated software or hardware. It also minimizes the chances of being left unsupported when manufacturers cease to provide patches and support for older products, thus adding an extra layer of protection against potential cybersecurity threats.
Understanding Product End-of-Life (EOL): A Key Aspect of Device Lifecycle Management

The lifecycle management of computer devices isn’t just about determining when to replace or repair them. It also involves a clear understanding of the concept of product end-of-life (EOL). EOL is a term used to denote the stage in a product’s life cycle when the manufacturer decides to stop supporting it, which means no more updates, patches, or any form of support will be provided.
Being aware of the EOL dates of their devices is vital for businesses, as they need to plan to replace these devices before support ceases. By doing so, they can mitigate the risk of potential security threats and system vulnerabilities that can arise from using outdated software and hardware. This approach forms a crucial component of proactive device lifecycle management.
How LogicFortress Can Be Your Trusted Ally
Managing device lifecycles effectively requires a well-planned strategy, technical expertise, and a deep understanding of your business’s specific needs. This is where LogicFortress (DNS) can assist. At DNS, we offer a comprehensive suite of IT services, including device lifecycle management, ensuring your business’s devices are always up-to-date, secure, and functioning efficiently.
Our team of seasoned experts can guide you through product EOLs, helping you replace devices well before support ends, and eliminating the risk of using unsupported software or hardware. With our tailored approach, we work closely with you to understand your device needs, develop a lifecycle management plan that suits your specific requirements, and implement this plan efficiently.
Whether you need assistance with device lifecycle management, or have queries about our services, we are just a call away. Our team is always ready to provide you with optimal IT solutions that meet your business needs, ensuring that your IT infrastructure remains a robust pillar supporting your business success, rather than becoming a point of vulnerability. Reach out to us today, and let us help you navigate the challenging world of device lifecycle management effectively and efficiently.






