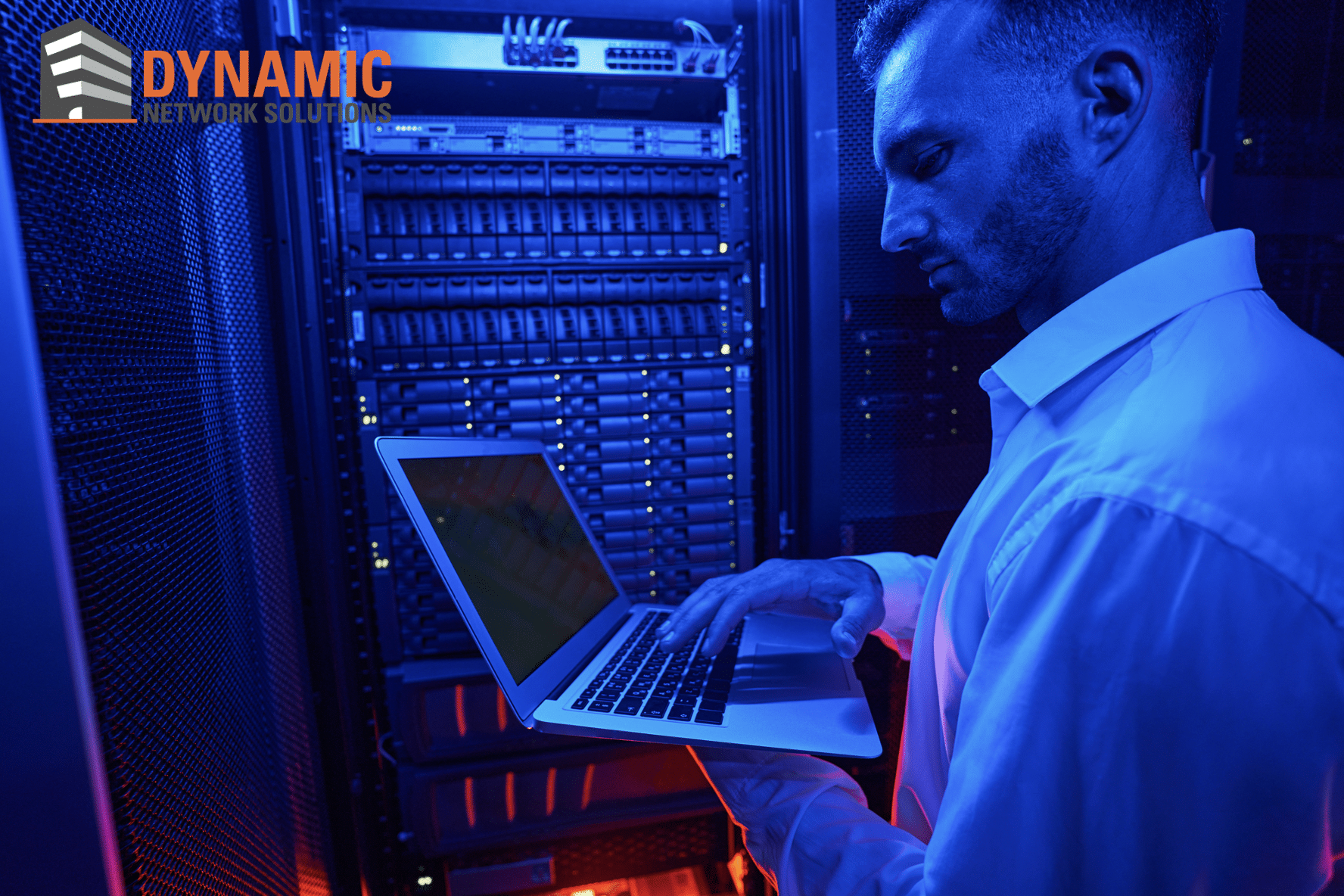
In today’s digitally-driven world, a reliable and efficient network is not just a luxury—it’s a necessity for any thriving business. When your network is running smoothly, your employees can perform their tasks without interruption, ultimately saving time and increasing productivity. However, even minor network issues can have a major impact, leading to frustrated employees, dissatisfied customers, and even lost profits.
We’re here to shed light on five common network issues that can slow down your business operations. We’ll provide practical solutions for each problem to help you get your network—and your business—running at peak performance again.
The Importance of Network Uptime for Business Operations
Network uptime, or the amount of time your network is up and running, is a critical metric for business success. It’s not just about keeping the lights on; it’s about ensuring that your business operations continue unhindered.
Why Network Uptime Matters:
- Customer Satisfaction: In an age where customer experience is king, a slow or broken network can turn away potential clients.
- Employee Productivity: Time lost due to network downtime translates directly to decreased productivity and increased operational costs.
- Data Integrity: Consistent network performance is essential for data backup processes, and even minor disruptions can compromise the integrity of your business data.
- Competitive Advantage: A well-maintained network can give you an edge over competitors who may be struggling with downtime issues.
By prioritizing network uptime, you’re investing in the stability and reliability of your entire operation.
Issue 1: Slow Internet Speed
One of the most common network issues businesses encounter is slow Internet speed. In our fast-paced digital world, slow Internet is not just a minor annoyance; it’s a productivity killer. Whether it’s sluggish load times for essential applications or a buffering video conference call, slow Internet speed can have a detrimental impact on various aspects of daily operations.
Common Reasons for Slow Internet Speed
- Overloaded Network: Too many devices connected to the same network can create congestion, slowing down the Internet for everyone.
- Outdated Hardware: Old routers, switches, or modems can’t handle high-speed Internet effectively.
- ISP Issues: Sometimes, the issue may not be in your control and could be a result of poor service from your Internet Service Provider (ISP).
Practical Solutions and When to Seek Professional Help
- Upgrade Internet Plan: If your Internet speed isn’t sufficient for your business needs, consider upgrading your plan.
- Optimize Network Configuration: Simple changes in your network settings can sometimes dramatically improve speed. Consult your IT team to ensure optimal configuration.
- Prioritize Traffic: Modern routers allow you to prioritize network traffic so that essential applications get the bandwidth they need.
- Seek Professional Help: If you’ve tried the above solutions and still experience slow speeds, it may be time to consult network professionals for a more in-depth diagnosis and solution.
By understanding the reasons behind slow Internet speed and knowing how to tackle them, you can significantly reduce downtime and increase productivity.
Issue 2: Frequent Disconnections
Few things are more frustrating in a workday than dealing with frequent network disconnections. When your network is unstable, it not only affects your immediate tasks but can also disrupt the workflow of the entire organization, leading to missed deadlines and increased operational costs.
Common Reasons for Frequent Disconnections
- Hardware Malfunction: Sometimes, the router or the network card can be the culprit, causing frequent drops in the connection.
- ISP Issues: At times, the problem lies with the Internet Service Provider, particularly if the service is inconsistent.
- Overloaded Network: Too many devices connected to a single network can also lead to frequent disconnections.
Troubleshooting Tips and Long-term Solutions
- Check the Hardware: Ensure that all networking hardware is functioning as it should. Look out for any loose cables or overheating routers.
- Contact Your ISP: If you suspect the issue is from their end, it might be worth giving them a call to inquire about any outages or maintenance.
- Network Monitoring: Employ network monitoring solutions that alert you before problems become critical. This allows for proactive management of network issues.
If the disconnection issues persist or are causing significant operational disruptions, it may be time to seek the expertise of a professional network support team to diagnose and resolve the issue.
Issue 3: Security Vulnerabilities
Common Security Loopholes
- Open Wi-Fi Networks: A network without password protection can easily be accessed by anyone, including hackers.
- Outdated Software: Failing to update your network software regularly leaves you exposed to known security flaws.
- Weak Passwords: Simple or default passwords can easily be cracked, giving unauthorized users access to your system.
The Implications
The consequences of security vulnerabilities can range from minor inconveniences to severe setbacks, such as:
- Loss of confidential data
- Financial losses due to fraud or ransomware
- Legal consequences from compromised customer data
Solutions and Best Practices
To secure your network effectively, consider the following:
- Regular Software Updates: Always keep your network’s firmware and software updated to the latest version.
- Strong Password Policies: Implement strong, unique passwords and change them regularly.
- Multi-Factor Authentication (MFA): Use multiple forms of verification before granting access to your network.
- Professional Network Audits: For a thorough assessment, consider hiring professionals to evaluate your network’s security.
Taking these proactive measures will not only strengthen your network’s defenses but also instill greater confidence in your clients and stakeholders, assuring them that their data is safe and secure.
Issue 4: Inadequate Backup Systems
One often overlooked aspect of network support is the implementation of effective backup systems. A poorly managed or non-existent backup system can spell disaster for a business, especially in scenarios such as data loss, hardware failure, or cyber-attacks like ransomware.
Typical Backup Shortcomings
- Manual Backups: Relying solely on manual backups can lead to human error or missed backup schedules.
- Local Only Storage: Storing backups only on local devices can be disastrous in case of physical damage or theft.
- Lack of Versioning: Without multiple versions of files, you risk losing important data changes or updates.
The Ripple Effect
The lack of a robust backup system can have far-reaching consequences, including:
- Permanent loss of critical data
- Disruption of business operations
- Wasted time and resources in data recovery attempts
Steps to Ensure Robust Backup
To build a resilient backup system, consider the following best practices:
- Automated Backups: Schedule regular automated backups to eliminate human error.
- Cloud-Based Solutions: Utilize cloud storage for secure, remote backups.
- Version Control: Implement a version control system to preserve changes over time.
- Testing: Periodically test your backups to ensure they can be restored successfully.
Having a foolproof backup system is not a luxury but a necessity for any business serious about its data and operations. By investing in a robust backup system, you safeguard your business against unexpected data loss and ensure uninterrupted business continuity.
Issue 5: Inadequate Security Measures
In today’s digital landscape, cybersecurity isn’t just an IT issue; it’s a business imperative. A lapse in network security can lead to unauthorized access, data breaches, and even legal consequences, severely affecting your business reputation and bottom line.
Common Security Gaps
- Outdated Software: Running outdated software leaves your network vulnerable to exploitation.
- Weak Password Policies: Easy-to-guess passwords can be a goldmine for attackers.
- Unsecured Devices: Employee personal devices can become entry points for network intrusions.
Consequences of Lax Security
Ignoring or overlooking security can lead to:
- Confidential data leaks
- Financial losses due to fraud or ransom
- Legal penalties and reputation damage
Strengthening Your Security Posture
Here are some proactive steps to bolster your network’s security:
- Regular Updates: Always keep your software and security protocols up-to-date.
- Strong Password Policies: Enforce complex passwords and multi-factor authentication.
- Device Management: Have a policy in place for managing and securing employee devices.
- Network Monitoring: Continuously monitor network activity to detect and address unusual behavior.
By implementing stringent security measures, you not only protect your business assets but also instill confidence among your clients and stakeholders that their data is in safe hands.
The Importance of Proactive Network Support
 In an era where business continuity heavily depends on reliable network performance, ignoring common network issues is a risk no organization should take. From slow internet speed to inadequate security measures, these challenges can bring day-to-day operations to a grinding halt, affecting productivity and profitability.
In an era where business continuity heavily depends on reliable network performance, ignoring common network issues is a risk no organization should take. From slow internet speed to inadequate security measures, these challenges can bring day-to-day operations to a grinding halt, affecting productivity and profitability.
However, many of these issues are preventable or manageable with the right approach:
- Timely Upgrades: Keep your hardware and software up-to-date to ensure optimal performance.
- Regular Monitoring: Stay vigilant and proactive in identifying and addressing potential problems.
- Professional Assistance: When in doubt, seek the help of experts in network support to avoid escalating problems into catastrophes.
By adopting a proactive approach to network support, you can ensure smoother operations, better security, and ultimately, a more successful business. So, don’t wait for a crisis to happen. Take charge of your network health today.




